[en-gb] ⚠️ Important Disclaimer
1️⃣ Some time ago, I recorded a course on cloud security in Microsoft environments for a Brazilian university called IGTI. This course was part of a Cloud Computing bootcamp and helped many students who were just starting their careers in the field. (After the institution shut down, the content became unavailable.)
🎯 So, I decided to remaster, sanitize, and re-release this content for free on YouTube, with the goal of continuing to support those who are beginning their journey in Cloud and Cloud Security.
2️⃣ The original course is in Portuguese (pt-BR), but throughout the series I’ll also publish articles in English (en-US) so the content can reach more people — at least until the new courses in English are recorded and ready.
3️⃣ Important: this series is not certification prep and not a silver bullet.
The goal here is to share structured knowledge, with a hands-on, accessible approach focused on:
- Cloud beginners,
- Security enthusiasts, and
- Anyone looking to better understand how Azure actually handles security.
4️⃣ Microsoft has rebranded some of its products — for example, Azure Security Center is now Defender for Cloud, and Azure Active Directory is now Entra ID. Some lessons may still refer to the old names, but don’t worry — the core concepts, technical foundations, and functionalities remain the same. Focus on the architecture and principles being taught.
Hope you enjoy it! Big hug!
Gustavo Magella
🎬 Watch Episode #02 of 09 Now
🔗 Click here to watch on YouTube – Episode 02 of 09.
(And yes, hit that subscribe button. I’m watching… 👀)
[EN-US] Beyond The Cloud – Spin-Off | Chapter 02: Access & Identity Security in Azure
Hey, what’s up folks!? Back for another chapter? Good. Because today we’re unlocking one of the most crucial layers of cloud security: Access and Identity in Azure. And if you’re still thinking passwords are enough — this post might just save your environment.
Let’s be honest: if attackers can bypass your identity controls, it doesn’t matter how many firewalls you’ve set up. Identity is the new perimeter. And that’s where we begin.
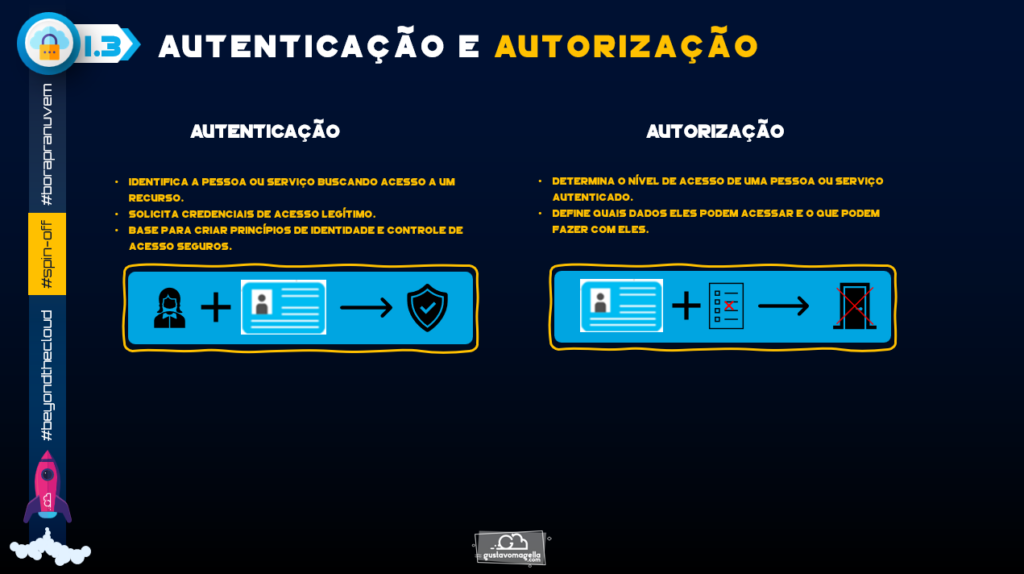
🔐 Auth vs. Authz: Know the Difference
Let me paint a scenario for you:
Imagine Cristóvão Colombo (our brave test user) logs into your Azure tenant. He enters his credentials and gets in. Boom! He’s authenticated.
But wait — can he view resources? Can he create a VM? Can he delete a storage account?
That’s authorization.
- Authentication: Proves who you are. It’s the door key.
- Authorization: Determines what you can do once inside. It’s which doors you’re allowed to open.
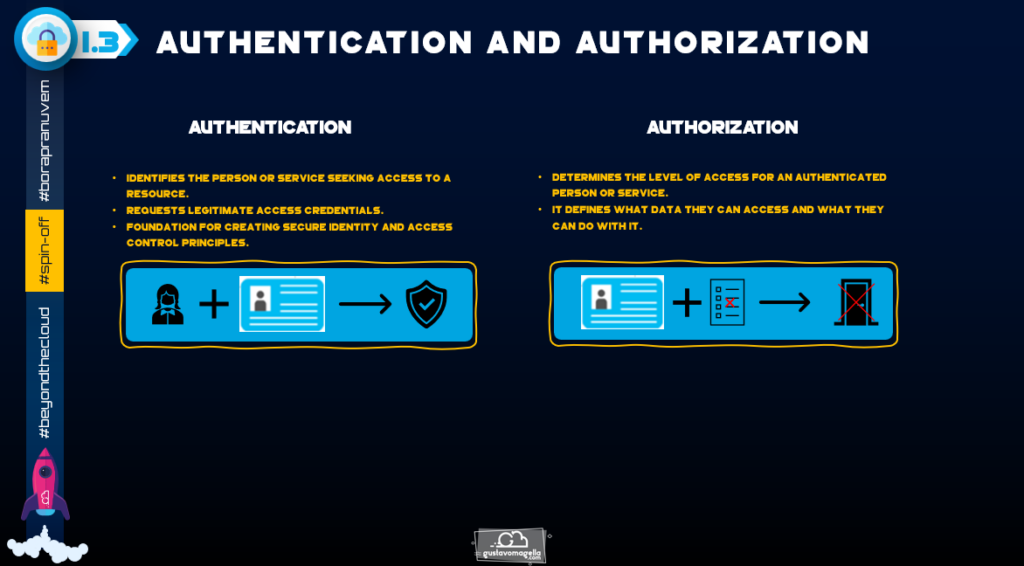
Don’t confuse the two. They walk together, but have different purposes.
🪑 Azure Active Directory (Now Microsoft Entra ID)
We all remember the classic AD from on-prem days. Microsoft Entra ID is that — evolved, modernized, cloud-native, and powerful.
Some features you should be leveraging:
- SSO for seamless access across services;
- App registration and management;
- Guest access (B2B) for external collaboration;
- Device identity and compliance policies;
- Conditional Access for dynamic access control;
In practice: You can bulk create users, manage groups, assign roles, invite guest users, and fine-tune their access.
And here’s a pro tip:
Directory roles are different from RBAC roles. Keep that separation clear.
Colombo as a basic user? He can log in and read some details. Colombo as a Global Administrator? That man can light the whole place on fire.
🧱 MFA: Multi-Factor Authentication, The Right Way
Still running single-factor logins in your cloud environment? That’s like leaving your front door open with a sign that says “Please knock.”
Azure gives you free MFA, no P1 or P2 license required. And here’s how it works:
- Something you know (Password or PIN);
- Something you have (Phone, token, smartcard);
- Something you are (Biometrics);
I always recommend using the Microsoft Authenticator App — QR code, setup, push notifications. Done.
But don’t stop there. Configure fallback options: SMS, phone call, and backup admins. Losing access to MFA shouldn’t mean panic.
🕵️ RBAC: Role-Based Access Control
Now let’s talk power and permissions.
RBAC in Azure is surgical. It lets you grant exactly the right access at exactly the right scope. But if you mess up? You either give too much (disaster) or too little (frustration).
RBAC =
- Security Principal: Who? (user, group, service principal);
- Role Definition: What? (read, write, delete, manage);
- Scope: Where? (Management Group > Subscription > Resource Group > Resource);
Give Colombo Reader access to a VNet if all he needs is visibility. Giving him Owner at the subscription level? You’re giving him the nuclear codes.
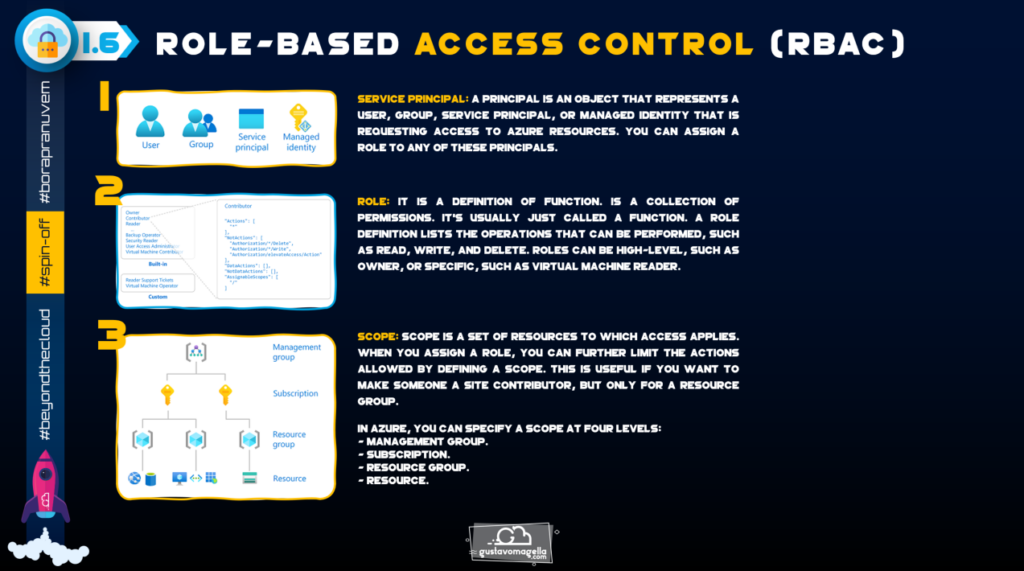
You want fine control? Use Access Control (IAM) on each resource. Assign, audit, adjust.
Remember: roles cascade downward. If you assign at the subscription level, every child resource inherits it.
👁️ Real-World Chaos: Colombo Goes Wild
Let’s say you made Colombo an Owner at subscription level “just for a test.”
He now sees everything. All three resource groups, all the networks, all the VMs.
He clicks “delete” on a VNet. No prompt. No warning. Gone.
Next time you look, half your infra is gone. And Colombo? He just wanted to see how things worked.
✨ Naming Policies & Group Management
Want to stop users from creating groups called “Test123” or “Cool Admins”?
Define naming conventions, restrict keywords, and enforce structure. Also:
- Assign managers to accounts
- Use group nesting
- Define security groups vs M365 groups appropriately
Assign Cabral as part of the “Navegadores” group, report to Colombo, and you’ve got a neat, auditable structure.
🪖 Practical Checklist
- ✅ Enable MFA for all users (even guest users);
- ✅ Review sign-in logs monthly;
- ✅ Audit RBAC assignments and scopes;
- ✅ Avoid default roles; use custom where possible;
- ✅ Always use the principle of least privilege;
- ✅ Keep naming structured and logical;
📊 My Tech Two Cents
If identity is your front door, MFA is the lock, and RBAC is your house key distribution system.
No point in using biometric locks if everyone gets the master key.
Train your team. Document everything. And never — ever — give subscription-level Owner access casually.
📆 Coming Up Next…
In Chapter 03, we’ll tackle Network Security in Azure:
- NSGs;
- Azure Firewall;
- DDoS Protection;
You’re gonna love it.
Much love, and secure that identity perimeter! 🌹❤️
Gustavo Magella
[pt-br] ⚠️ Um aviso importante:
1️⃣ Há um tempo, eu gravei um curso de segurança em nuvem focado em ambientes Microsoft para uma universidade brasileira chamada IGTI. Esse curso fazia parte de um bootcamp de Cloud Computing e, na época, ajudou muitos alunos que estavam começando suas jornadas na área. (Com o fechamento da instituição, o conteúdo acabou ficando indisponível.)
🎯 Sendo assim, resolvi remasterizar, sanitizar e re-lançar esse conteúdo gratuitamente no YouTube, com o objetivo de continuar ajudando quem está começando na área de Cloud e Cloud Security.
2️⃣ O curso original está em português (pt-BR), mas ao longo da série vou publicar também artigos em inglês (en-US), para que o conteúdo possa alcançar mais pessoas até que os novos cursos em inglês estejam gravados e disponíveis.
3️⃣ Importante: essa série não é preparatória para certificações e não é uma bala de prata.
A proposta aqui é compartilhar conhecimento de forma estruturada, com uma pegada prática e acessível, voltada para:
- Iniciantes em Cloud,
- Entusiastas de segurança, e
- quem busca entender melhor como o Azure trata segurança de verdade.
4️⃣ A Microsoft renomeou alguns de seus produtos — por exemplo, o Azure Security Center agora se chama Defender for Cloud, e o Azure Active Directory virou Entra ID. Em algumas aulas, os nomes antigos ainda aparecem, mas foquem nos conceitos e fundamentos técnicos, que continuam válidos e extremamente relevantes.
Espero que vocês gostem! Um forte Abraço!
Gustavo Magella
[PT-BR] Beyond The Cloud – Spin-Off | Capítulo 02: Segurança de Acesso e Identidade no Azure
E aí, seus trens bonitows!? Se preparem que hoje o trem é sério. Vamos falar sobre o alicerce da segurança em nuvem: a identidade.
Sim, aquele velho ditado mudou: Identidade é o novo perímetro.
Esse tipo de insight é ouro. E é sobre isso que vamos falar ao longo da série.
🎬 Assista o Capítulo 02
🔗 Assista agora no YouTube – Capítulo 02 de 09
(E se inscreve no canal, senão vou saber que você pulou essa parte… rs)
🔐 Autenticação vs Autorização
Autenticação: você é você mesmo? Digitou sua senha?
Autorização: beleza, agora que você entrou, o que você pode fazer aqui dentro?
Não adianta autenticar se você libera acesso total pra quem não deveria.
🪑 Azure AD virou Entra ID — e tá cada vez mais robusto
Com o Microsoft Entra ID, você pode:
- Criar e gerenciar usuários (em massa inclusive)
- Convidar terceiros (guest users)
- Configurar roles de diretório (diferentes das RBAC de recurso)
- Monitorar logins e atividades
Colombo como user normal? Vê o que precisa. Colombo como Global Admin? Sai de perto.
🧱 MFA: o novo mínimo
Senha sozinha não segura mais nada.
Com o MFA gratuito da Microsoft, você já consegue proteger todo seu tenant.
Use os 3 pilares:
- O que você sabe (senha)
- O que você tem (celular, token)
- O que você é (biometria)
Configure o Microsoft Authenticator, escaneia o QR code, escolhe as opções. E crie alternativas: SMS, chamada, etc.
🕵️ RBAC: acesso na medida certa
No Azure, a autorização é feita via RBAC. Ela é composta por:
- Security Principal: o “quem”;
- Role Definition: o “o quê”;
- Scope: o “onde”;
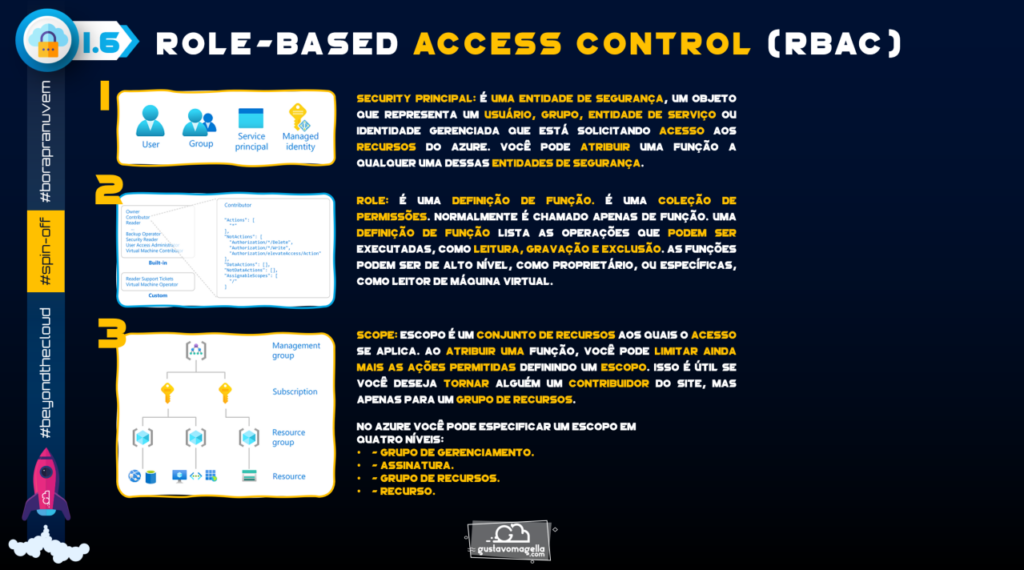
Exemplo clássico:
- Colombo precisa ler uma VNet?
- Dê a ele Reader só nela. Não na Subscription inteira.
Lembre-se: roles herdadas viram uma dor de cabeça rápido.
👁️ Colombo invadiu tudo? Deu mole
Se você der permissão de Owner na subscription, ele consegue ver tudo. E deletar tudo. Sem aviso!!
Você precisa de controle granular. RBAC é poderoso, mas perigoso.
✨ Nomeação e Grupos
Crie padrões de nomeação. Evite grupos chamados “admin geral” ou “teste”.
- Nomeie gestores (manager)
- Use hierarquia de grupos
- Restrinja roles ao máximo
🪖 Checklist Rápido
- ✅ MFA habilitado pra todo mundo! (Sem excessões!)
- ✅ Log de login revisado; (Um olho no peixe, outro no gato)
- ✅ RBAC sob controle;
- ✅ Nada de Owner de graça; (De preferência use o PIM)
- ✅ Naming e grupos bem definidos; (Padronize, sempre que possível)
📊 Minha Tech Two Cents
⭐ Segurança começa na identidade.
⭐ MFA é o cadeado. RBAC é quem tem chave de cada porta.
⭐ Não adianta usar biometria se você dá a chave-mestra pra todo mundo.
📆 Próximo Capítulo
Capítulo 03: Segurança de Rede no Azure
- NSGs;
- Azure Firewall;
- DDoS Protection;
Vai ser insano!!!!! lol #borapranuvem
Um bjo no coração e se cuidem! 🌹❤️
Gustavo Magella